Enhancing IT Workflows: Managed Service Providers Near Me at Your Service
Wiki Article
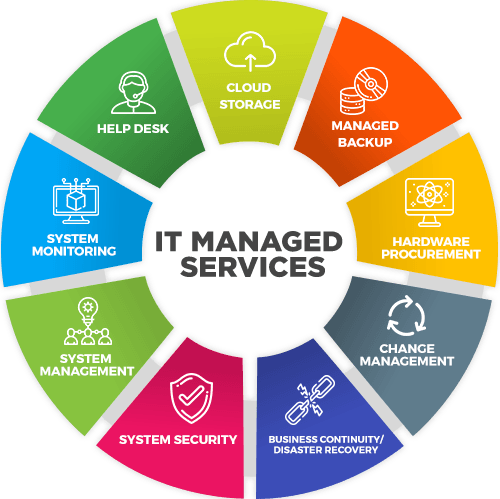
Strategize and Range WITh Proven IT Managed Services Approaches
In the fast-paced landscape of modern service, the tactical application of IT managed solutions has come to be a foundation for companies aiming to boost functional efficiency and drive lasting development. By applying proven strategies tailored to meet specific service demands, business can navigate the complexities of innovation while remaining agile and affordable in their corresponding industries. As the demand for scalable IT services remains to climb, comprehending just how to effectively strategize and utilize took care of services has never been more important. It is within this realm of innovation and optimization that services can absolutely unlock their potential and pave the way for future success.Advantages of IT Took Care Of Provider
By outsourcing IT administration to a specialized service provider, companies can tap right into a wide range of knowledge and resources that would certainly otherwise be costly to keep internal. One of the essential benefits of IT Handled Services is aggressive monitoring and upkeep of systems, which aids stop possible problems before they rise into significant troubles.This makes sure that businesses continue to be affordable in a quickly progressing technological landscape. In conclusion, the benefits of IT Managed Solutions are important in improving operations, enhancing efficiency, and ultimately, driving organization success.
Key Techniques for Implementation
With an understanding of the significant benefits that IT Managed Services offer, organizations can now focus on carrying out key strategies to successfully integrate these services right into their operations. One crucial approach is to plainly define the extent of services required. This includes conducting an extensive analysis of existing IT framework, recognizing discomfort points, and establishing particular goals for enhancement. Furthermore, businesses should establish clear communication channels with their taken care of company to make certain smooth partnership and prompt concern resolution.One more essential strategy is to focus on cybersecurity steps. Information breaches and cyber threats posture considerable risks to services, making safety and security a leading priority. Implementing durable security methods, regular surveillance, and prompt updates are important actions in protecting delicate info and keeping company connection.
Additionally, organizations ought to develop service degree arrangements (SLAs) with their handled provider to specify assumptions, obligations, and efficiency metrics. SLAs help in setting clear standards, ensuring responsibility, and keeping service high quality criteria. By incorporating these crucial approaches, companies can take advantage of IT Took care of Services to improve procedures, boost efficiency, and drive sustainable development.
Making The Most Of Effectiveness With Automation
In addition, automation makes it possible for real-time tracking and data analysis, providing valuable understandings for educated decision-making. By automating regular tracking tasks, businesses can proactively resolve concerns prior to they escalate, minimizing downtime and optimizing efficiency (managed service providers). In addition, automation can assist in the seamless assimilation of various systems and applications, improving collaboration and information flow across the company
Ensuring Data Security and Conformity
Information safety and security and conformity are critical problems for companies running in the digital landscape of today. With the raising volume of delicate information being stored and refined, ensuring robust safety measures is vital to safeguard against cyber dangers and stick to regulatory needs. Implementing extensive information security practices includes securing information, establishing gain access to controls, consistently updating software, and carrying out security audits. Conforming with laws such as GDPR, HIPAA, or PCI DSS is essential to avoid costly penalties and maintain count on with customers. Managed IT providers play an important function in assisting companies navigate the complex landscape of data security and conformity. They supply expertise in implementing security methods, checking systems for possible violations, and guaranteeing adherence to industry regulations. By partnering with a reliable managed providers, organizations can improve their data security stance, alleviate dangers, and demonstrate a dedication to securing the confidentiality and integrity of their information possessions.
Scaling IT Facilities for Development
Incorporating scalable IT facilities remedies is vital for facilitating service development and operational effectiveness. As firms expand, their IT needs progress, resource calling for infrastructure that can adjust to raised demands perfectly. By scaling IT facilities properly, organizations can guarantee that their systems continue to be reliable, protected, and performant also as work expand.One trick aspect of scaling IT facilities for growth is the capability to flexibly allot sources based upon current requirements. Cloud computing services, as an example, deal scalability by permitting organizations to readjust storage space, refining power, and other resources as needed. This elasticity enables companies to efficiently manage spikes sought after without over-provisioning resources during periods of lower activity.
Moreover, implementing virtualization technologies can enhance scalability by managed service provider enabling the creation of virtual circumstances that can be conveniently copied or changed to suit altering workloads - managed service providers. By virtualizing web servers, storage space, and networks, organizations can optimize resource utilization and simplify IT monitoring procedures, eventually supporting business development efforts successfully
Final Thought
Finally, implementing IT took care of solutions can bring various benefits to a company, such as boosted effectiveness, enhanced information safety, and scalability for growth. By following vital methods for implementation, making use of automation to make best use of effectiveness, and guaranteeing information safety and compliance, organizations can better plan and scale their IT facilities. It is important for organizations to advance and adapt with technical developments to remain competitive in today's ever-changing landscape.
Report this wiki page